cxf证书式安全验证。第一步 生成可用的数字证书 使用命令行打开您要生成数字证书的路径
生成证书还是比较麻烦的,要用到jdk的一个工具——keytool 首先,创建客户端KeyStore和公钥 在命令行运行: 1、创建私钥和KeyStore: keytool -genkey -alias clientprivatekey -keypass keypass -keystore Client_KeyStore.jks -storepass storepass -dname “CN=tongtech.com,C=CN” -keyalg RSA
创建KeyStore,文件名字为Client_KeyStore.jks,里面有个名为clientprivatekey的私钥。 2、给私钥进行自签名: keytool -selfcert -keystore Client_KeyStore.jks -storepass storepass -alias clientprivatekey -keypass keypass
签名成功,无任何提示。 3、导出私钥 作用是导出的证书将作为公钥保存到TrustStore中。 keytool -export -alias clientprivatekey -file Client_PublicCert.cer -keystore Client_KeyStore.jks -storepass storepass
如果成功,可以看到提示: 保存在文件中的认证 <Client_PublicCert.cer> 然后创建服务端KeyStore 1、创建私钥和KeyStore keytool -genkey -alias serverprivatekey -keypass keypass -keystore Server_KeyStore.jks -storepass storepass -dname “CN=tongtech.com,C=CN” -keyalg RSA
2、给私钥进行自签名 keytool -selfcert -keystore Server_KeyStore.jks -storepass storepass -alias serverprivatekey -keypass keypass
3、导出私钥 keytool -export -alias serverprivatekey -file Server_PublicCert.cer -keystore Server_KeyStore.jks -storepass storepass
接下来,将客户端公钥导入到服务端TrustStore中,将服务端公钥导入到客户端TrustStore中。 在命令行中输入: keytool -import -alias clientpublickey -file Client_PublicCert.cer -keystore Server_TrustStore.jks -storepass storepass
回车后会提示
引用
所有者:CN=tongtech.com, C=CN 签发人:CN=tongtech.com, C=CN 序列号:4cc7e86c 有效期: Wed Oct 27 16:53:00 CST 2010 至Tue Jan 25 16:53:00 CST 2011 证书指纹: MD5:FB:AB:71:9F:56:F3:CB:65:16:DC:52:E0:2D:27:FF:F6 SHA1:06:A8:B1:B4:E2:42:9D:B2:F7:99:E7:70:34:08:96:52:E1:CD:4A:76 签名算法名称:SHA1withRSA 版本: 3 信任这个认证? [否]:
打y即可,然后提示
引用
认证已添加至keystore中
同理,将服务端公钥导入到客户端TrustStore中 keytool -import -alias serverpublickey -file Server_PublicCert.cer -keystore Client_TrustStore.jks -storepass storepass 同样会出现提示,打y回车,提示成功就可以了。 最终你会在您的文件夹中看到如下的文件 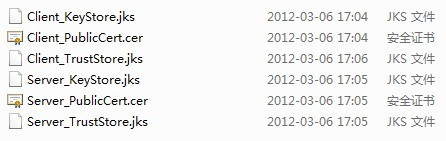
第二步 服务端配置 1.放置证书的位置和属性配置 将上面生成的文件以Server开头的文件放置在src的cert包下 配置Server_Decrypt.properties,内容如下 org.apache.ws.security.crypto.provider=org.apache.ws.security.components.crypto.Merlin org.apache.ws.security.crypto.merlin.keystore.type=jks org.apache.ws.security.crypto.merlin.keystore.password=storepass org.apache.ws.security.crypto.merlin.keystore.alias=serverprivatekey org.apache.ws.security.crypto.merlin.file=cert/Server_KeyStore.jks 这里有个问题要注意,要注意去除空格,否则会报org.apache.ws.security.components.crypto.Merlin Not Found的error 配置Server_Verf.properties,内容如下 org.apache.ws.security.crypto.provider=org.apache.ws.security.components.crypto.Merlin org.apache.ws.security.crypto.merlin.keystore.type=jks org.apache.ws.security.crypto.merlin.keystore.password=storepass org.apache.ws.security.crypto.merlin.keystore.alias=clientpublickey org.apache.ws.security.crypto.merlin.file=cert/Server_TrustStore.jks 2.设置配置文件(由于在上一篇文章已经有了基本的配置,这里直接给出WSS4JInInterceptor的配置) <bean id=”WSS4JInInterceptorCert” > <constructor-arg> <map> <entry key=”action” value=”Signature Encrypt” /> <entry key=”signaturePropFile” value=”Server_SignVerf.properties”/> <entry key=”decryptionPropFile” value=”Server_Decrypt.properties”/> <entry key=”passwordCallbackClass” value=”ws.interceptor.UTPasswordServerCallBack”/> </map> </constructor-arg> </bean> 3.UTPasswordServerCallBack类

- import java.io.IOException;
- import javax.security.auth.callback.Callback;
- import javax.security.auth.callback.CallbackHandler;
- import javax.security.auth.callback.UnsupportedCallbackException;
- import org.apache.ws.security.WSPasswordCallback;
- public class UTPasswordServerCallBack implements CallbackHandler {
- public void handle(Callback[] callbacks) throws IOException,
- UnsupportedCallbackException {
- WSPasswordCallback pc = (WSPasswordCallback) callbacks[0];
- pc.setPassword(“keypass”);
- System.out.println(“Server Identifier=” + pc.getIdentifier());
- System.out.println(“Server Password=” + pc.getPassword());
- }
- }
import java.io.IOException;
import javax.security.auth.callback.Callback;
import javax.security.auth.callback.CallbackHandler;
import javax.security.auth.callback.UnsupportedCallbackException;
import org.apache.ws.security.WSPasswordCallback;
public class UTPasswordServerCallBack implements CallbackHandler {
public void handle(Callback[] callbacks) throws IOException,
UnsupportedCallbackException {
WSPasswordCallback pc = (WSPasswordCallback) callbacks[0];
pc.setPassword("keypass");
System.out.println("Server Identifier=" + pc.getIdentifier());
System.out.println("Server Password=" + pc.getPassword());
}
}
第三部 客户端配置 1.放置证书的位置和属性配置 将上面生成的文件以Client开头的文件放置在src的cert包下 配置Client_Encrypt.properties,内容如下 org.apache.ws.security.crypto.provider=org.apache.ws.security.components.crypto.Merlin org.apache.ws.security.crypto.merlin.keystore.type=jks org.apache.ws.security.crypto.merlin.keystore.password=storepass org.apache.ws.security.crypto.merlin.keystore.alias=serverpublickey org.apache.ws.security.crypto.merlin.file=cert/Client_TrustStore.jks 配置Client_Sign.properties,内容如下 org.apache.ws.security.crypto.provider=org.apache.ws.security.components.crypto.Merlin org.apache.ws.security.crypto.merlin.keystore.type=jks org.apache.ws.security.crypto.merlin.keystore.password=storepass org.apache.ws.security.crypto.merlin.keystore.alias=clientprivatekey org.apache.ws.security.crypto.merlin.file=cert/Client_KeyStore.jks 2.设置配置文件(由于在上一篇文章已经有了基本的配置,这里直接给出WSS4JOutInterceptor的配置) <bean id=”WSS4JOutInterceptorCert”> <constructor-arg> <map> <entry key=”action” value=”Signature Encrypt”/> <entry key=”user” value=”clientprivatekey”/> <entry key=”signaturePropFile” value=”Client_Sign.properties”/> <entry key=”encryptionUser” value=”serverpublickey”/> <entry key=”encryptionPropFile” value=”Client_Encrypt.properties”/> <entry key=”passwordCallbackClass” value=”ws.erp.UTPasswordClientCallBack”/> </map> </constructor-arg> </bean> 3.UTPasswordClientCallBack类

- public class UTPasswordClientCallBack implements CallbackHandler {
- public void handle(Callback[] callbacks) throws IOException,
- UnsupportedCallbackException {
- WSPasswordCallback pc = (WSPasswordCallback) callbacks[0];
- pc.setPassword(“keypass”);
- System.out.println(“Client Identifier=” + pc.getIdentifier());
- System.out.println(“Client Password=” + pc.getPassword());
- }
- }